Comcast owes me money. They owe lots of people money.
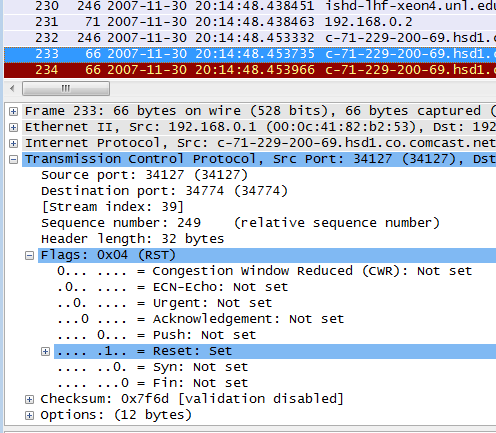
In 2007 and 2008 Comcast forged TCP RST packets in order to throttle P2P and other kinds of traffic. This resulted in several class-action lawsuits. They recently settled one of them and agreed to pay each affected customer $16.
From an individual perspective this isn’t a lot. However, for those who are eligible for the settlement I have a proposal: submit your claim form and make it part of a larger donation to your local food bank or homeless shelter.
That’s what I’m going to do.